Germany - Amsterdam Aesthetics originally published at Germany - Amsterdam Aesthetics

Prioritizing might be one of the most difficult tasks in #cybersecurity. How do you deal with thousands of vulnerabilities?
— Kevin Townsend
MIAMI, FLORIDA, UNITED STATES, January 18, 2023 /EINPresswire.com/ — How to easily select exploitable vulnerabilities that could most expose or hurt organization’s infrastructure? It is the question of how to prioritize efficiently. We know that customers need context information to reduce hundreds of critical vulns into a few and have more time to center their attention on what really matters.
Vulnerability management is an ever-changing field, with new threats and new solutions popping up all the time. The challenge is choosing the right way to handle vulnerabilities without getting buried in complexity. Finding the right tool is key to success.
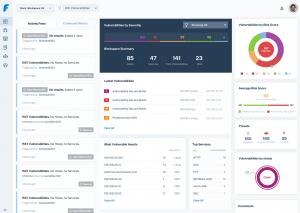
Faraday Platform uses risk score, a feature that allows prioritization in the vulnerability management process, so it doesn’t grow out of control. By the end of this article, the overall objective is to know how to simplify the process.
Any long-term vulnerability management process should have three key characteristics: First, it should be strategic — meaning it should have the security team’s resources in mind. Prioritizing smartly is a must; we aim to reduce the time our customer spends on minor issues and focus on the ones that matter most. Second, it should be repeatable — meaning they should be able to repeat the process again and again with consistent results. No organization can afford to wing it when managing vulnerabilities, especially in today’s hyper-connected digital world. Third, it should be efficient — meaning that taming the avalanche of findings should take less time. A proactive approach is superior to a reactive one.
Which vulnerabilities should businesses focus on first? This is the most common question when working with new clients. Everyone wants to know which vulnerabilities are critical and worth focusing on. It’s a valid question, but it can also be misleading. Most companies have a list of thousands of vulnerabilities they need to fix because the CVSS treats all assets equally. So they try to prioritize that list based on the risk the vulnerability poses to their organization. Without considering those three additional factors – asset value, trending, and weaponization – they might end up patching vulnerabilities that aren’t likely to be exploited and leaving others that could expose even more sensitive assets if left unpatched. Faraday’s risk score job is to identify each asset in terms of its risk and critical value.
“Various research shows that companies can have more than 100,000 vulnerabilities in their systems, but 85% cannot realistically be exploited.”
The urgency of a vulnerability is not always directly proportional to its risk. For example, noisy, frequent, and non-urgent vulns can be categorized as high but hardly exploitable. Faraday provides a score that shows the risk for each and gives context. This risk score is calculated based on the likelihood of a vulnerability being exploitable and the number of times it is mentioned on Twitter. This gives your organization a deeper insight into the vulnerability’s massivity and importance. Any company should take all these aspects into account when prioritizing and use all this information to make an informed decision and work mindfully and on your own terms. The vulnerabilities that have the highest likelihood and the highest impact should be your top priority.
It can be tempting to try to fix everything at once. After all, that’s what most organizations hope to do. That’s why prioritizing vulnerabilities that are exploitable is so essential. Faraday Security Platform helps security teams make the most of their time and resources by focusing on what truly matters. And also get ahead of the curve rather than playing catch-up. Faraday help build a stronger, more resilient organization that can better withstand attacks and breaches in the future.
Faraday Security
Faraday Security
+1 904-715-4284
email us here
Visit us on social media:
Facebook
Twitter
LinkedIn
Instagram
YouTube
TikTok
Other
![]()
Germany - Siver News originally published at Germany - Siver News
The post How to deal with cyber threats in today’s world with the same security team and avoid burnout first appeared on Amsterdam Aesthetics.
Germany - Amsterdam Aesthetics originally published at Germany - Amsterdam Aesthetics